As in any industry, the business models that drive asset management are constantly changing. These increasingly complex transformations are frequently linked to the relentless need to reduce costs and often result in the delegation of activities. Regulatory requirements also tend to favor the separation of roles to increase transparency and ensure greater operational efficiency while reducing risk to investors.
In their article “Differentiating Control, Monitoring and Oversight” from September 2017, Margaret M. Cullen (Institute of Banking, Dublin) and Niamh M. Brennan (University College Dublin, Ireland) outline clear distinctions between Control, Oversight and Monitoring.
- Monitoring provides the transparency required by fund promoters and investment fund boards for their fund activity.
- Control is the daily process performed by fund operators on their operational activities.
- Oversight is the capacity to check the accuracy of operational, monitoring and control functions, including that of activities delegated to third parties.
Regardless of what we might wish, the simplistic or utopian “integrated front-to-back” model simply cannot satisfy these obligations. Each “puzzle piece” within an organization has its own information system. Each plays a part in the overall process of reconciliation, oversight, monitoring, control, and verification.
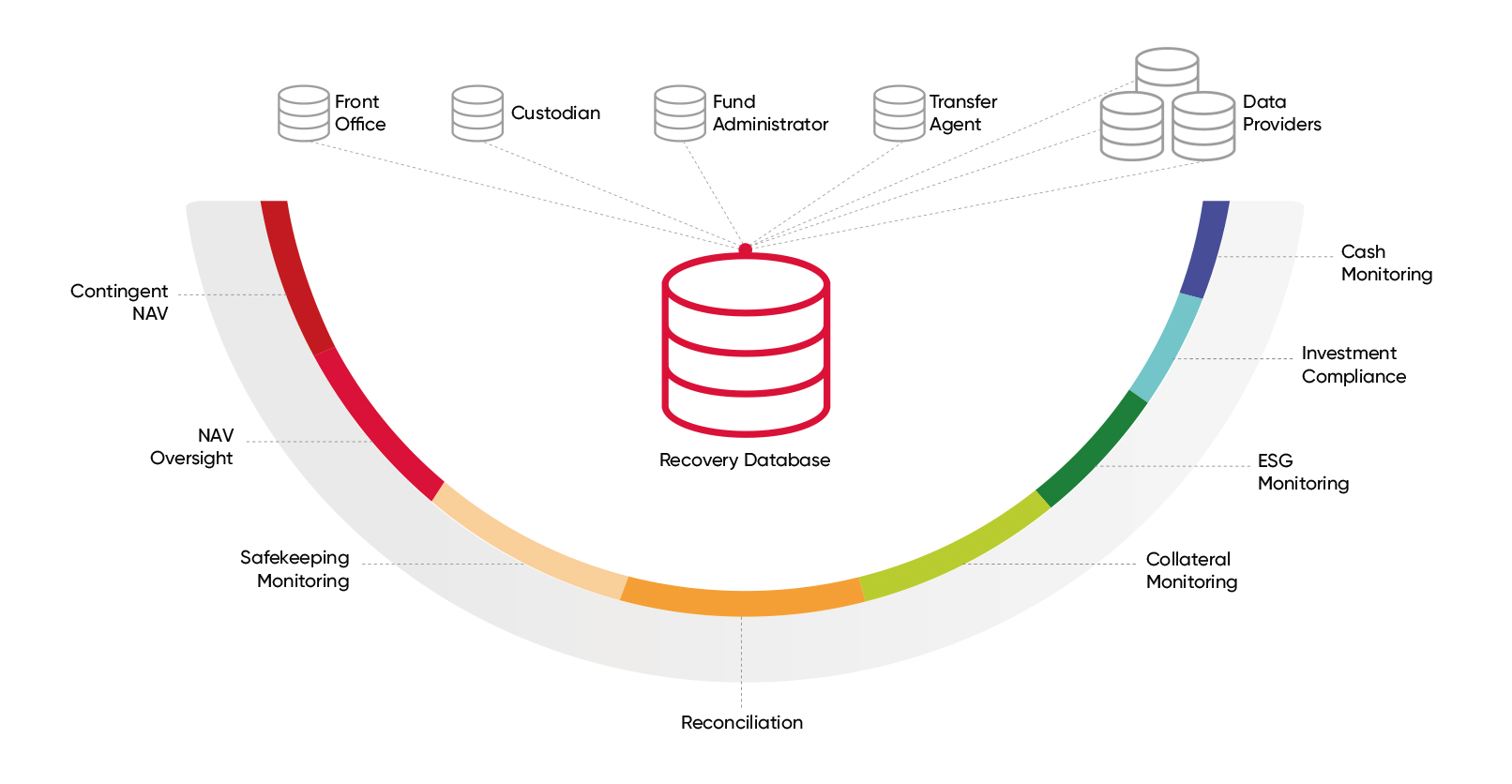
Establishing a central ‘RECOVER’ controls repository that includes each of these parts would provide for better REconciliation, Compliance, and OVERsight outcomes, while reducing license and implementation costs. Doing so, however, presents a real challenge!
The sum of many individual parts
Like organs or systems within a living organism, each part of a firm’s front, middle or back office is equipped with specialized teams that rely on largely automated processes. These constantly check that the global system is coherent, accurate and homogeneous while facilitating the correct working of each individual part.
The reputation of each unit is at stake, but so is the super-set represented by the sum of these parts. The slightest error can be paid for in cash: a poorly adjusted portfolio can give rise to unexpected transactions, a poorly calculated NAV can result in colossal repayments, and poorly monitored cash positions can give rise to ill-considered abuses.
But first, what do we mean by control of “operational risks”?
The fund industry is subject to numerous risks, including credit, counterparty, market, liquidity, and operational risk. Automating controls over certain operational risks is challenging, although “machine/deep learning” mechanisms are showing promise in this regard. More broadly, the funds industry has implemented numerous automated and manual checks to guard against fraud and reduce the reputational and financial risk related to non-compliance and tax issues and the breakdown of information systems and operational processes.
The ALFI and ABBL Guidelines and Recommendations for Depositaries, published by ALFI and ABBL in 2018, set out the control and oversight responsibilities of custodians and management/investment companies as follows: “While the depositary is responsible for the control of its primary duties, the management/investment company remains responsible for oversight of actions carried out by its delegates and has to deal with issues identified and settle them in the best interest of its unitholders/shareholders.”
“RECOVER(Y)” in action
Let’s take for example the legal or statutory control of investment ratios. These are calculated at the Front Office level (in pre-trade mode) and again at the Middle Office level (in post-trade mode) and then sometimes produced by Custodian Banks or Fund Administrators on behalf of the Management Companies.
The same goes for NAV controls, which are carried out either by the Fund Administrators or the Management Companies (which then monitor activities delegated to the Fund Administrators).
And then you have cash reconciliation and monitoring between Custodians and Fund Administrators, Custodians and Transfer Agents, or between Fund Administrator and Custodian portfolios. This web of interlocking activities can be summarized by this basic scheme.
With the best will in the world, the great difficulty with these operational controls is that they are dispersed across different organizational and informational layers which make them cumbersome to manage and digest. Firms may struggle to manage these controls adequately, resulting in compliance rules deficiencies and weaknesses as outlined in a recent paper from the US Securities and Exchange Commission’s Office of Compliance Inspections and Examinations.
The responsibility for ‘getting it right’ is not always shared by all constituents, yet all face some degree of reputational (and at times financial) risk at the prospect of getting it wrong.
So, it’s challenging. And if 35 years in the business have taught me anything, it is that that we need more than hollow statements like: “IT systems must adapt to the structural evolution of their environment.”
But in conclusion, I would like to leave you with my view on the framework for future success in operational risk management.
Building a strong operational risk mitigation structure
Many oversight, reconciliation and compliance software applications have been developed over the past 20 years, but these often failed to respect the following five pillars of robust operational risk mitigation programs:
- Preventing GIGO: to avoid “Garbage in, Garbage Out”, control tools must always be separate from the operational system.
- Cost of redundancy: control tools should avoid fragmentation and concentrate data in a unique ‘golden source’ database.
- Global management oversight: Managers must be able to assess risk at a glance using centralized dashboards.
- Maintenance cost: control tools should use a common infrastructure (rules, dashboards, and reporting) for all types of controls.
- Control and workflow accuracy: although each type of control (compliance, NAV, cash, et cetera) may have specificities we cannot ignore, all must be accurate and transparent.
In a world where workflows are increasingly integrated while workforces are ever more dispersed, asset managers and their application and service providers must work harder than ever to mitigate operational risk.
Let us hope that innovative software developers will take the lead in considering operational risk holistically. If they do, maybe soon this ideal dashboard concentrating operational risks will be available!

About the author, Henri Berthe

Henri Berthe is a Senior Product Manager at Linedata, with over 25 years of experience in the investment fund and asset management software industry. His expertise includes Compliance, Risk, NAV Oversight, and Cash Monitoring for UCITS and AIF.
Investment Compliance and Fund Oversight
Linedata helps leading firms like yours conduct robust pre-trade and post-trade compliance and fund oversight. Learn more about our portfolio compliance and NAV Oversight solutions.



